ENERGY SECTOR UNDER ATTACK
ELECTRIC GRID, PIPELINE NETWORK AND POWER PLANTS DEAL WITH MORECYBERTHREATS THAN THE FINANCIAL SECTOR
By Drew Robb
Figure 1: Email is now the top cyberattack vector into organizations[/caption]
Late last year, several Ukrainian power companies experienced unscheduled power outages, with malware known as BlackEnergy (BE) discovered on the computer networks of many organizations involved in the nation’s infrastructure. The U.S. immediately dispatched an investigatory team comprised of representatives from agencies such as the National Cybersecurity and Communications Integration Center, Department of Energy, Federal Bureau of Investigation, and the North American Electric Reliability Corporation.
A joint investigation with Ukrainian authorities came to the conclusion that this was caused by external cyber-attackers. Power outages were the result of remote cyber intrusions at three regional electric power distribution companies impacting about 225,000 customers. The attack was synchronized and coordinated, probably following extensive reconnaissance of the victim networks. A series of attacks occurred within 30 minutes of each other and impacted multiple central and regional facilities. Malicious remote operation of the breakers was conducted by multiple external hackers using either existing remote administration tools at the operating system level or some form of remote industrial control system (ICS) software. The perpetrators acquired legitimate credentials prior to the cyberattack to facilitate access. At the conclusion of the attack, some systems were impacted by KillDisk malware which deletes or corrupts selected files. The Uninterruptable Power Supplies (UPS) was also sabotaged via remote management, interfering with restoration efforts.
Under attack
The energy sector, it turns out, is attacked more than other critical infrastructure industries, according to U.S. Department of Homeland Security (DHS) incident response statistics. Exelon’s experience backs this up. “We see many attempts on our environment, but we haven’t been impacted by any headline events to date,” said Samara Moore, Senior Manager of Critical Infrastructure Protection (CIP) Security and Compliance at Exelon.
The power and oil & gas industries can expect an increasing frequency of such attacks going forward. The pipeline sector, said Moore, may not be a major target of attackers, but it provides a way to disrupt a region or divert attention so they can go after another target. “Supervisory Control and Data Acquisition (SCADA) systems have end points and control centers that are geographically dispersed, thereby presenting a possible target,” said Moore.
Attackers or threat actors include nation states, competitors, organized crime, script kiddies (one who uses existing exploits or scripts to hack; they are often, but not always young), hacktivists, insiders and terrorists. Their motivations may be financial, industrial, military, ideological, political, retribution and prestige. Assets that might potentially come under threat include: SCADA, programmable logic controllers (PLCs), communication networks, intellectual property (IP), users, infrastructure, business plans, user devices and customer lists. “Failing to deal with such threats could affect reputation, revenues and the brand image,” said Moore. “It can also lead to regulatory fines, competitive disadvantage and distraction from major objectives.”
Her advice is to be proactive, not to only attempt to deal with such issues as they come up. Unfortunately, the lines of infiltration are many and hard to prevent. A recent study by Osterman Research found email to be the top attack vector into organizations, with web-based attacks second (Figure 1) (Sidebar).
Technology alone is not enough to manage cyber security risks to industrial control systems, she said. It has to be backed up with trained personnel resources and the appropriate organizational processes. This includes best practices for remote access management, supply chain risk management, gaining awareness of current threats and grooving in sufficient agility to respond quickly. Fortunately, there is no need to reinvent the wheel. Several security frameworks already exist that can be adapted to industry. For example, the NIST Cyber Security Framework, the IEC 62443 Industrial Automation Systems Security, and the Oil and Natural Gas Subsector Cybersecurity Capability Maturity Model (ONG-C2M2) from the U.S. Department of Energy can be used to improve the cybersecurity capabilities of the energy sector. They can help organizations evaluate, prioritize, and improve security responsiveness.
“Such frameworks help organizations prevent the majority of attacks, as well as leveraging technology and expertise to detect intrusions,” said Moore. “Based on the event, you can then respond by evaluating the scope of the incident, contain it effectively and then conduct mitigation and remediation activities.” Exelon utilizes the Cyber Kill Chain (CKC) methodology, developed by Lockheed Martin. This recognizes seven stages of an attack that have to be completed by an adversary in order to be successful: Recon, weaponization, delivery, exploitation, installation, command control and action on objectives. Moore said that the best approach is to detect and prevent these efforts as early in the kill chain as possible. The earlier you are able to detect them, the lower the remediation costs will be.
“Cyberthreats to pipeline systems are real and can have a major impact,” said Moore. ‘What’s more, we have an increased frequency of attacks on ICS in the face of a growing skills gap.” But just hiring security experts isn’t enough for the energy sector. Those individuals lack the know-how of power plants, pipeline networks and industrial infrastructure in general. So they may not comprehend the purpose of an attack or the best way to prevent it. “Security personnel may not understand your world so communicate with them and make your area real to them so they can protect it adequately in a way that works for you.” said Moore.
Sidebar: WEB-BASED ATTACK MODES
Phishing: Phishing is a play on the word “fishing.” Phishing emails are sent to large numbers of users simultaneously and attempt to “fish” sensitive information from unsuspecting users by posing as reputable sources. This includes banks, credit card providers, delivery firms and law enforcement. Their ploy is to trick the user into either clicking on a link to infect the PC, open an infected attachment or go to a fake website to enter login credentials, financial information, social security data or credit card details. But any data entered is likely to be used maliciously to steal money or an identity, or infiltrate a network. According to the Verizon 2015 Data Breach Investigations Report, 23% of recipients open phishing messages. Another 11% click on attachments.
Spearphishing: While phishing involves the transmission of one email to a large list, many of whom don’t even use that bank, credit card or service, spearphishing is targeted at specific individuals or a small group. The instigator has either studied up on the company or group, or has gathered intelligence from social media sites to gain enough data to con users. The originators use this data to make their messages more believable and increase the likelihood of success. And it’s a piece of cake, these days, to uncover basic data about employees from the web, Facebook, Twitter or LinkedIn. This can include travel plans, family details, employment history and various affiliations. Thus the open rate for spearphishing is far higher than that of phishing.
Executive whaling: This comes from the Vegas gambling term “whale” which means a high roller who is going to lay down some serious money. Cybercriminals are increasingly targeting executive whales, who are surprisingly easy to get to open suspicious emails. Perhaps due to their hefty volume of traffic, they don’t have the time to look closely before they click. In some cases, thieves have managed to wangle millions of dollars out of corporate accounts. In the power or oil & gas field, some unsuspecting plant manager might be fooled into shutting a facility down after receiving a spoof email from his boss.
Watering holes: A watering hole is a place you tend to go to frequently and which is trusted. This might be a regularly used website, a business partner’s portal or a vendor marketplace. By compromising that location, the bad buys seek to piggy pack into the corporate network.
Newsletter
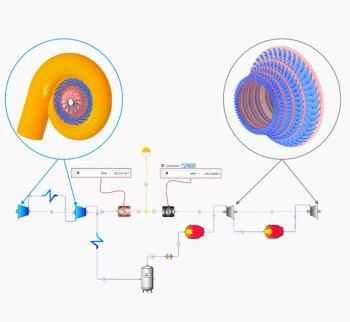
Power your knowledge with the latest in turbine technology, engineering advances, and energy solutions—subscribe to Turbomachinery International today.